See below: NNSA Cyber education programs
The amount of valuable data guarded by the world’s networks is immense. At national laboratories, protected information is directly tied to the mission and to the nation’s infrastructure, so there’s no shortage of adversaries seeking to gain access to the data or bring down the systems.
The growing demand for cybersecurity professionals around the globe puts a premium on those in the industry and makes cybersecurity a critical skills area at Sandia. This situation also emphasizes the importance that Sandia places on helping to grow the number of talented individuals available to enter the cybersecurity pipeline.
GET SCET: cyber education
Capture the Flag is a game almost everyone knows, but the typical concept was flipped on its head this summer for the Sandia Cyber Educational Training, or GET SCET, Cyber Camp. Through this program, middle and high school participants captured “flags” in a series of cyber challenges that required them to apply knowledge they learned during several days of training.
As a member of the Consortium Enabling Cybersecurity Opportunities & Research Program, Sandia worked with the University of Virgin Islands to host a weeklong cyber camp in July for 41 students, including 16 from Albuquerque and 26 from the U.S. Virgin Islands.
Camp participants competed in the final GET SCET Capture the Flag event and, eventually, the national CyberPatriot competition sponsored by the U.S. Air Force Association. Over the course of four days, the students learned about networks, scripting, the Linux operating system, Windows systems and cryptography. When it was time for the competition, they received material and CTF questions developed by Sandia summer interns.

Casey Haynes, one of the summer interns from New Mexico Tech, provided technical insight into how his work with Sandia’s Tracer Forensic and Incident Response Exercise, or Tracer FIRE, Program helped him contribute to the camp. “The GET SCET material that I authored mostly had to do with using and configuring Linux-based operating systems,” he said.
“A lot of the Linux infrastructure setup I was involved with in the Tracer FIRE program helped me in writing the GET SCET material, namely in the specific area of configuring Linux security settings (configuring iptables, file and directory permissions, etc.).”
Enter the pandemic. In a normal year, activities like GET SCET would be conducted in a collaborative learning environment, but Sandia and its partners refused to be thwarted from their educational mission by COVID-19.
Sandia’s Research and Engineering Cyber Operations and Intelligence Lab, or RECOIL, and development team partnered with the University of New Mexico and UVI to transform their program into a virtual STEM experience where students could learn and enjoy the thrill of the competition.
UNM’s Virtual Reality Lab hosted online virtual machines for participants, and Sandia provided detailed video lectures and electronic lab content so students could learn at their own pace up to the competition. When it was finally time for students to capture the flags, Sandia interns from N.M. Tech, the University of Colorado, Boulder, and UVI manned a live support chat to ensure all participants could ask questions as needed.

“Manning the chat desk was an interesting and rewarding experience,” said Shadron Gudmunson, a volunteer from N.M. Tech. “It was challenging at times, since not all of the students knew how to explain what problems they were having, and it usually took some coaxing to figure out what they were actually having issues with. But when they eventually got it figured out, it was great to see them get even more sucked in (to the experience).”
Following the GET SCET cyber camp competition, Jair Smith, an academic coach for UVI, said, “Our territory’s very own Mireille Boumedine achieved first place in the competition. Other students also indicated they would love to participate in these programs again.”
The students’ comprehension of the overall GET SCET content was backed up by data from surveys conducted after the cyber camp. Results showed a 29% growth in the number of students who indicated they understood a lot about general cybersecurity concepts, and a 53% growth in students who said they understood a lot about the importance of cryptography in cybersecurity.
These and other metrics demonstrate that the funding for the NNSA’s Consortium Enabling Cybersecurity Opportunities & Research Program from the Minority Serving Institutions Partnership Program is paying real educational dividends.
When presented with obstacles, the development team did what the Sandia workforce always does — they forged a new path along with others who were invested in the same successful outcome. At the end of the camp, the students walked away with a basic understanding of the skills they need to pursue a cybersecurity career.
Tracer FIRE challenges students
Sandia’s Tracer FIRE Program incorporates the competitive thrill of GET SCET, exponentially building on those skills for the university students and industry professionals who take part in the training.
The Tracer FIRE team works with academic institutions to provide students with realistic experiences so they understand what it takes to be on the front lines of the cyber war. Over the course of three days, Sandia experts on the Tracer FIRE team produce cyber incident response scenarios featuring different advanced persistent threat adversaries.
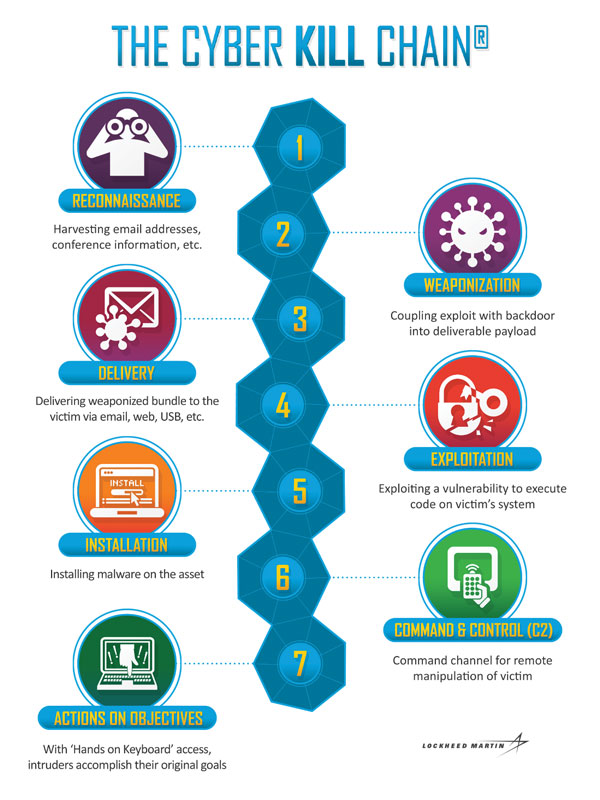
Participants then have the rest of the time each day to figure out the cyber kill chain by identifying the adversary, how they got into the network, what they wanted, whether they acquired it, and ways to prevent similar incidents from reoccurring.
The Tracer FIRE Program uses narrative-based learning, which provides participants with meaningful context for the training content and helps to further cement the new information and processes in their minds. In the network environments constructed by Sandia, participants can safely interact with live malware while recognizing adversarial tactics within the context of the kill chain. Knowing how to confront these exact types of situations will be critical to the students if they continue in the field.
Tracer FIRE and other events such as GET SCET take Sandia’s RECOIL team a lot of time and effort to organize and execute, but it’s an investment Sandia believes will pay dividends by fueling the much needed cybersecurity talent pipeline.
Turning up the Tracer FIRE heat
Over the summer, Sandia’s Tracer FIRE team had multiple opportunities to work with local academic institutions in developing and executing the program, and also in growing the potential impact of Tracer FIRE across the country.
One important lead-in to Tracer FIRE’s summer started in the spring when Linnea Sands, Sandia Academic Alliance technical partnerships development specialist, approached Marcus Chang, director of cybersecurity and mission computing, with a proposal to stand up a Sandia Research Institutes pilot at New Mexico Tech. Marcus immediately saw the merit and helped to facilitate funding and management support.
N.M. Tech Director of Cybersecurity Centers and principal investigator Lorie Liebrock selected the students using criteria offered by the Sandia managers over Computer Systems Security Analysis Research & Development and Cyber Enterprise Security. Liebrock had already arranged for her research group to work remotely, so the transition to Sandia’s Tracer FIRE team was seamless, even in the midst of COVID-19.
“The students worked full-time through mid-August on two projects,” Liebrock said. “They also enhanced existing Tracer FIRE scenarios and created new ones for a Capture the Flag event held this summer.”
The N.M. Tech students also worked with other Sandia interns to create challenges built around four educational areas for the advanced Tracer FIRE 10 program.

“For me, the Tracer FIRE program was a great introduction to working with cybersecurity directly for the first time,” said Elijah Aldinger, a participant from UC Boulder. “It was fulfilling to build the individual components for the platform and see them actually run and get used during the simulations.”
The Sandia RECOIL and development teams also met with participating N.M. Tech faculty and provided them with the needed infrastructure, including the virtualization and forensic analyst environments. They discussed how to design attack chains, write narrative storylines, run attack simulations, create Jupyter notebooks to allow for the creation and sharing of live code, and document threat reports.
Linnea, who helped facilitate the pilot, believes the collaboration between Sandia and N.M. Tech was successful in multiple aspects. “Helping students prepare for their future field takes real world application. The interns participating in the Sandia Research Institutes pilot were able to not only develop their own skills by working at the Labs, but able to parlay that experience by crafting content to help other individuals develop their abilities,” she said
The week of August 17, a Tracer FIRE Workshop training was held with a group of academic institutions, including the University of Illinois, Purdue University, North Carolina Agricultural & Technology State University, Norfolk State University, Auburn University, N.M. Tech, University of Maryland Baltimore County and Embry-Riddle Aeronautical University.
The Sandia team laid out the goals, structure and anticipated outcomes of the Tracer FIRE exercise and then highlighted how universities who chose to host an event could magnify the benefits by using a cascade mentoring strategy where their own students experience the exercise, learn how to plan a Tracer FIRE event, and then assist in teaching other students.
The Sandia team also walked through the logistical intricacies involved with putting on a virtual cyber event, which they had experienced for the first time when running the GET SCET camp in July.
Tommie Kuykendall, Sandia’s CECOR project manager who helped coordinate the workshop, said, “Events like these allow us to spread the word about all of the great things Sandia does and is about. Tracer FIRE, in particular, has been a great tool to connect with minority serving institutions across the country.”
NNSA Cyber education programs
Minority Serving Institutions Partnership Program
NNSA’s Minority Serving Institutions Partnership Program, instituted in 2015, is designed to build a sustainable pipeline between DOE sites and laboratories and minority serving institutions with STEM disciplines. The MSIPP program provides support to historically Black colleges and universities, tribal colleges and universities and Hispanic serving institutions, offering enrichment and development activities to help students succeed and make a smooth transition into a STEM career.
Consortium Enabling Cybersecurity Opportunities & Research Program
NNSA’s Consortium Enabling Cybersecurity Opportunities & Research Program is a cybersecurity education, internship and workforce partnership created in 2015 between Sandia, Lawrence Livermore National Laboratory and 13 HBCUs. It was awarded a five-year, $25M grant to help NNSA develop a K-20 pipeline of cybersecurity professionals to address a workforce shortage and increase the number of minority students pursuing cybersecurity careers.
The need for cybersecurity professionals is emphasized by projections that anticipate 3.5M cybersecurity job openings worldwide by 2021.
Thousands of students, from kindergarten age to college graduates, have been impacted by the broader consortium through cybersecurity education and training, K-12 programs, summer internships and bootcamps.
